![]() Cybersecurity Education Services
Cybersecurity Education Services
Prepare your organization for real-world cyber threats
Boost your organization’s ability to uncover, prevent, and resolve cyber incidents by providing your cybersecurity team and wider userbase with role-specific skills and awareness training. GLESEC combines cutting-edge gamified learning technology with expert human instruction and support to help your organization upskill everyone - even the most senior security analysts and threat hunters.
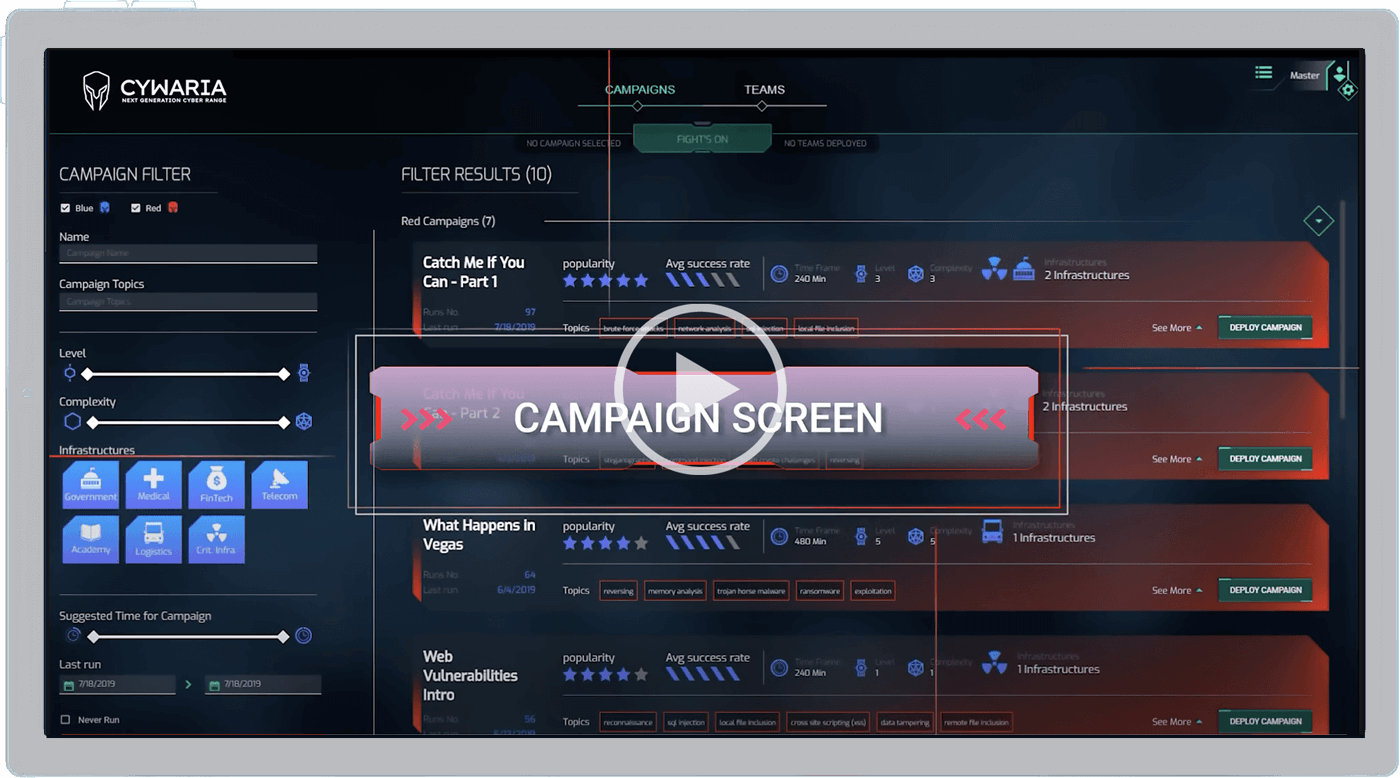
Click image to play video.
![]() Powerful, Realistic Training is the Only Solution
Powerful, Realistic Training is the Only Solution

PROBLEM
There aren’t enough skills to go around
The cybersecurity skills shortage leaves many organizations lacking vital skills and unprepared to protect their assets, data, and people.

SOLUTION
Military-grade skills training for any organization
GLESEC provides custom training scenarios - based on technology previously only available to the military and a few global enterprises - that include coordination, guidance, coaching, and debriefing.

IMPACT
Cyber resilience begins with skilled personnel
Our training services prepare your cybersecurity team and users for real-world threats like ransomware, phishing, and zero day vulnerabilities, so they can react quickly to a real attack.
![]() FAQs
FAQs
FAQ's

You ask, we answer!
Most MSSPs provide simple tools, sometimes with a basic management service. At GLESEC, we don’t believe this is enough to protect your organization against the ever-growing range of cyber threats.
We provide an intelligent combination of technology, management, and professional services tailored to your specific needs and infrastructure. Our services deliver the most comprehensive protection available anywhere—at a much lower cost than building in-house.
Most organizations have too many tools but lack the time and skills to properly configure or manage them. This results in a false sense of security, while still consuming precious time and resources.
GLESEC combines leading technologies with comprehensive managed and professional services to address your real business needs: easier compliance, accurate risk management, and greater resilience to cyberattacks.
We can do almost everything on your behalf - including responding to security incidents - based on pre-agreed rules of engagement. In a few cases, such as patching vulnerabilities in IT infrastructure, we provide full guidance and support to help your in-house team take the necessary steps.
For organizations with established incident response capabilities, we adapt our services to best support your existing personnel and workflows.
No. In most cases, it’s more cost effective to outsource cybersecurity to a trusted provider. Remember—it’s not just the cost of a tool to consider, it’s the total cost of configuring, managing, and maintaining that tool over it’s lifetime and replacing it next time you refresh your stack.
Here’s an example. A customer of ours once bought a tool instead of opting for our manage service equivalent. While the tool seemed cheap initially, the customer needed three staff to manage, maintain, and utilize it, making the tool a lot more expensive than our managed service.
![]() TECHNOLOGY PARTNERS
TECHNOLOGY PARTNERS
TOOLS BY THEMSELVES
ARE NOT ENOUGH TO PREPARE FOR REAL-WORLD CYBER THREATS
Start Honing Your Cybersecurity Skills
Find out how your organization can overcome the skills shortage with immersive training for cybersecurity teams and users.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.





