![]() Identity and Access Management Services
Identity and Access Management Services
Protect against privilege misuse, account takeover, and insider threats

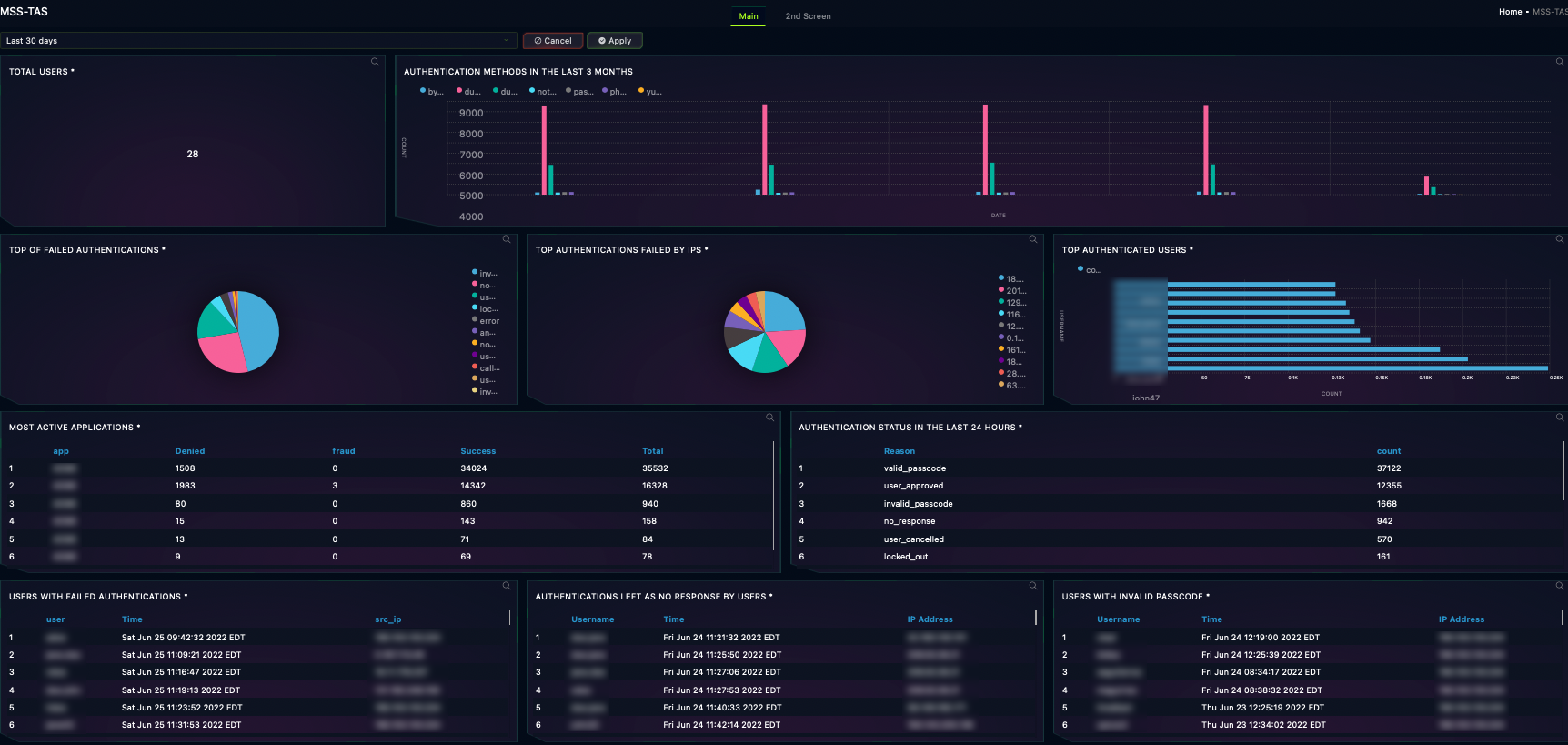
79% of enterprises experienced an identity breach in the last two years. GLESEC combines industry-leading technology with expert managed and professional services to protect your organization against all identity and access-based threats while ensuring a smooth user experience. Get up and running quickly with rapid onboarding and managed integration with any system.
Click image for more detail.
![]() The Fast and Simple Way to Reduce Cyber Risk
The Fast and Simple Way to Reduce Cyber Risk

PROBLEM
Traditional identity and access management techniques are dangerous
Most passwords are easily guessed or brute forced. Even strong passwords are vulnerable to theft via social engineering attacks. As a result, abuse of legitimate credentials is present in a huge proportion of today’s breaches.

SOLUTION
Replace passwords with a fully managed identity and access service
GLESEC combines smooth multi-factor authentication (MFA) with the industry’s leading privileged access management technology to provide fast, secure user authentication and tight access controls.

IMPACT
Make an attacker’s task much harder while protecting user experience
Protect your organization against identity and access-based threats and limit a persistent attacker’s ability to move laterally or escalate privileges—all while providing a seamless user experience.
Effortless Identity
and Access Management
Find out how your organization can protect against identity and access threats while maintaining a strong user experience.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.